Creating Trust Online
Comodo Containment Fused with Critical Endpoint Technology secures all your Servers, Desktops, Laptops, Tablets and Mobile devices from known and unknown Ransomware – without requiring signatures or updates. And, it supports Android, iOS, Windows systems, regardless of the type or age of the endpoint hardware.
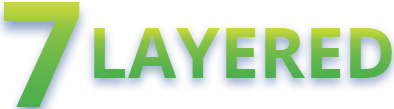
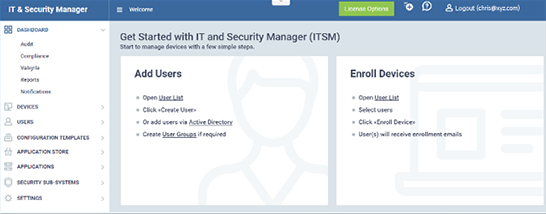
Whether it's lack of IT resources or the organizational strategy, many businesses find they need advanced protection made simple. Manage all the Devices from a Single Dashboard.
 Advanced Endpoint Protection
Advanced Endpoint Protection
Comodo Next-Gen Endpoint Protection (ITSM) software brings 7 layers of defense. Together under a single offering for customers of all sizes, to protect them from both known and unknown threats.

Unrecognized processes and applications are auto-sandboxed. They then run in a restricted environment.

This is an advanced interface which helps create rules as per the requirement-user-specific, sweeping, or granular.

This offers high-level security against inbound and outbound threats, protects computer's ports, manages network connections, and blocks confidential data transmission by malicious software.

Comodo Antivirus has notable features like multiple technology-based automatic detection, cleansing and quarantining of suspicious files. This helps detect and eliminate malware and viruses.

Cloud-based instant analysis of unknown files that checks file reputation against Comodo's master whitelists and blacklists.

This helps monitor important operating system activities to ensure protection against malware intrusion.

This is to monitor the behavior of all processes, which could help identify and prevent potential harmful action.
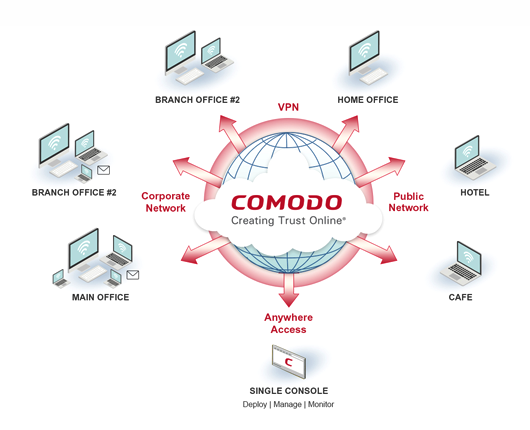
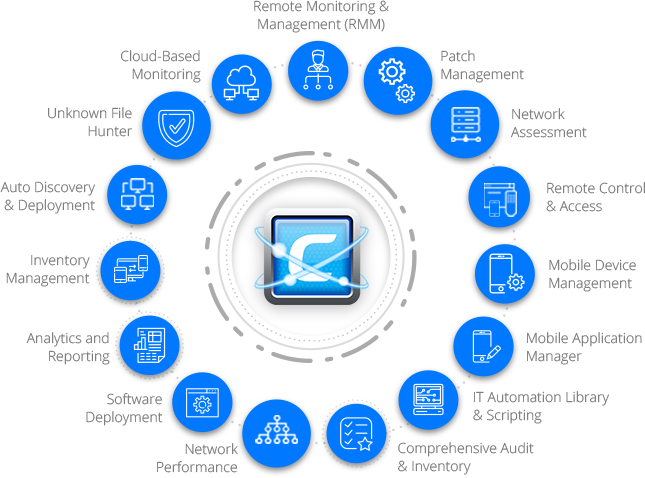
Delivers a layered suite of protection that is lightweight and scalable. Users can run any application on their endpoint with confidence, having only known good applications running on your network outside of containment.

Security is essential, but cost is still a consideration. Now you can have market-leading security for a cost-effective amount.
With Comodo Advance Endpoint Protection Securely manage all your endpoints
Please Contact Us
enterprisesales.india@comodo.com